An endpoint protection platform (EPP) is an integrated suite of endpoint protection technologies—such as antivirus, data encryption, prevention of intrusion, and prevention of data loss—that detect and stop a variety of endpoint threats. An endpoint protection platform (EPP) solutions are deployed on endpoint devices to prevent file-based malware attacks, to detect malicious activity, and to provide the investigation and remediation capabilities necessary to respond to dynamic security incidents and alerts. Endpoint protection is applicable to different types of endpoints to provide essential security ranging from smart phones to printers. Capabilities for the detection can vary, but advanced solutions use multiple detection methods, from static IOCs to behavioral analysis. EPP tools are mainly cloud-managed so that operation data can be constantly tracked and processed, along with the ability to take remote remediation steps, whether the source is on the corporate network or outside the workplace. Furthermore, these solutions are cloud-data-assisted, meaning that the endpoint agent doesn’t have to maintain a local database of all known IOCs, but can check a cloud resource to find the latest verdicts on objects it cannot classify.
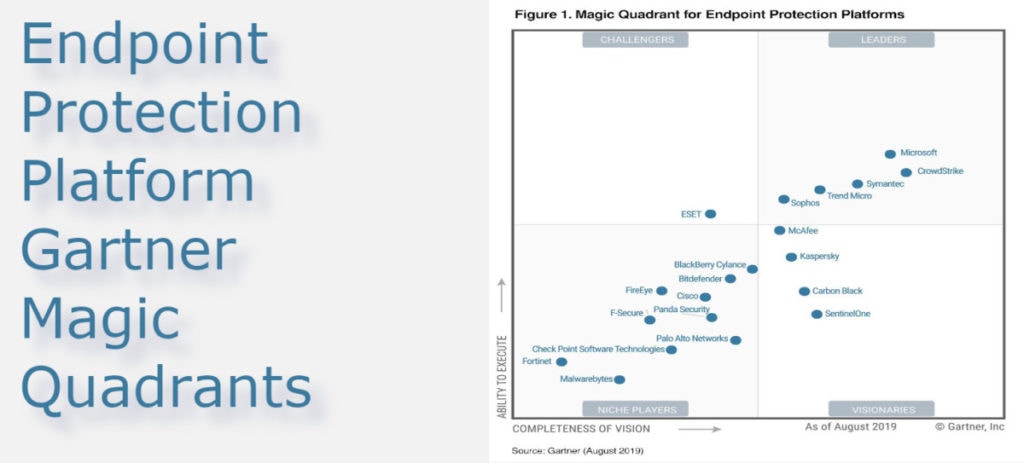
Endpoint protection platform – Gartner magic quadrants
Through the last few years, protection technology has evolved enormously by adding new features and enhancing existing ones.
- Multi-layer protection
- Threat analysis
- New approach to vulnerability management
- Cloud protection
- Behavioral observation
- Automated security
- advance threat protection (ATP)
The descriptions of the some of the best EPP tools are as follows:
Table of Content +
Microsoft Defender Advanced Threat Protection (ATP)
In Configuration Manager Hierarchy, Microsoft Endpoint Protection administers Antimalware policies and Windows Firewall security for client computers. Microsoft’s endpoint security platform, Microsoft Defender Advanced Threat Protection (ATP), has continuously evolved over the past few years by further enhancing existing features and adding new and innovative capabilities. You get the following advantages and features by using Endpoint Security with Configuration Manager:
Configure antimalware policies: Windows Firewall settings and manage advanced threat protection from Microsoft Defender to selected computer groups.
Multi-layered security: Microsoft Defender ATP offers multi-layered defense against file-based ransomware, malicious files, memory-based attacks and other sophisticated threats (built into the endpoint and cloud-powered).
Security analytics: Descriptive vulnerability assessments offer near-real – time insight to SecOps on how attacks impact their organizations.
A modern approach to handling threat and risk: real-time detection, market context-based prioritization and complex threat environment, and automated remediation processes speed up risk reduction and misconfiguration.
To update client computers: using Configuration Manager Program updates to access the latest antimalware description files.
Built-in, cloud-driven protections: Real-time threat detection and protection with built-in advanced capabilities protect against widespread and targeted attacks such as phishing and malware campaigns.
Behavioral detections: Endpoint detection and response sensor (EDR) integrated into Windows 10 for finer visibility into the kernel and memory, and the use of large credibility data for directories, IPs, URLs, etc.
“Deployment” is as easy as it gets being integrated directly into the operating system. There is no delivery team, no glitches or reliability problems and no increased overhead cost or conflicts with other products.
Send updates via email, using tracking in terminal, and view files. These actions inform administrative users upon detection of malware on client computers.
Contain the threat: Significantly reduce the risks when identifying external attacks, improving the defenses. Microsoft Defender ATP will immediately extend Conditional access to prevent the endpoint from accessing business data until the threat has been remedied.
Automated security: From alerts in minutes to mitigation-at scale. Microsoft Defender ATP uses AI to investigate alerts automatically, determine if a threat is active, what course of action to take, and then remedy complex threats in minutes.
Secure Score: Watch your Microsoft Defender Security Center security score rise as you implement automated, recommended actions to protect both users and data.
Crowd-strike Falcon Endpoint Protection
When it comes to achieving the endpoint security requirements, the Falcon Platform is one scalable and extensible solution that you can tr. Falcon Endpoint Protection bundle can be supplemented with the additional modules as well. Anyone can buy standalone modules and do not require complete Falcon Endpoints Protection bundle. Specialized solutions are designed for clients who deal under stringent compliance or operating criteria. Crowd strike Falcon was founded for two purposes; one is to protect all customers from every kind of cyber attack and the second is to remake security for the cloud era. In real-time, It uses artificial intelligence like machine signatures (Indicator of attack based) to prevent or block all unwanted and unknown signals/threats. Being acknowledged as a leader in the third year also for EEP in Gartner magic quadrant, crowd strike is one of the best solutions according to Gartner criteria like marketing strategies, vertical industry, innovation, and validity of the business model. Major features of crowd strike Falcon include:
Cloud Delivered Protection End Point by eliminating complexity, providing simplicity and flexibility and the use of crowd-sourced data and cloud analytics to combat emerging threats in real time.
Artificial Intelligence: Using the power of big data and artificial intelligence to allow the team to visualize and secure instantly during the life cycle of the threat.
Delivers The Required Protection: Provides all with a single, lightweight agent you need to avoid breaches. Provides replacement of antivirus, improves agents and restore endpoint efficiency.
https://www.crowdstrike.com/endpoint-security-products/
McAfee Endpoint Security
McAfee, the endpoint security market leader, provides a broad variety of solutions that incorporate strong endpoint defense with efficient endpoint management. Accelerated protections, increased efficiency and better management allow security teams to address more threats with less resources more quickly. McAfee updated its security endpoint offering to deliver a consolidated defense platform that makes investigations easier and enables one-click correction across the whole organization. McAfee eliminates silos between once-isolated capabilities to improve efficiency and protection by means of a single-agency architecture with deep integration and automation. With a single control console, McAfee Endpoint Protection combines established solutions such as firewall, reputation and heuristic technology with advanced machine intelligence and containment into a single platform agent along with EDR. The optimized endpoint security program guarantees users are productive, connected, and zero-day malware such as ransomware is stopped before the first endpoint is infected. McAfee Endpoint Security is only one component of open integration structure, enabling organizations to detect the whole continuum – from device to cloud – and to correct that.
https://www.mcafee.com/enterprise/en-us/products/endpoint-security.html
Apex One Endpoint Security (Trend Micro)
Trend Micro Apex One provides defense against ever-growing threats, including fileless malware and ransomware, through advanced automatic threat identification and response. Cross generational mix of modern techniques offers highly sophisticated endpoint protection that maximizes performance and efficiency. Using an integrated EDR toolset, SIEM integration and an Open API toolkit, you can receive actionable insights, extended analysis functionality and centralized visibility. You can conduct threat investigation via integrated and extended EDR or by expanding the managed service option for your security teams. Apex One provides a single agent for threat identification, response and investigation. Eliminate multiple vendors and consoles and gain flexibility in deployment via both SaaS and on site. Apex One uses a combination of cross-generational techniques for defending from all kinds of attacks in the widest possible range providing:
- Pre-execution machine learning and runtime machine learning
- Noise cancelation – such as census and white listing – throughout each detection layer to dramatically reduce false positive factors
- Advanced and accurate detection of malware, such as fileless, ransomware and cryptomining
- Effective protection against scripts, injection, ransomware, memory and browser attacks by innovative analysis of behavior
https://www.trendmicro.com/en_us/business/products/user-protection/sps/endpoint.html
Symantec Endpoint Protection Software
Symantec Endpoint Security is a completely cloud-managed Symantec Endpoint Protection on-site application offering multi-layer protection to deter attacks regardless of how they target the endpoints. It offers unified management across physical and virtual platforms with enhanced flexibility and scalability in terms of grid security policy controls. Symantec’s Endpoint Protection is designed to achieve high-performance efficiency and enables hardware to run more rapidly, and lasts longer for performance, and runs on several operating systems, including Windows, Linux and MacOS X. Symantec Endpoint Security is handled by Symantec Integrated cyber security Manager (ICDm), a single, challenging cloud platform that uses various tools to control the organizational security. Symantec Endpoint Protection provides protections for the attack including — pre-attack, attack, breach, and post attack– on Windows, Mac, Linux and other handheld devices. Symantec’s Endpoint Security Protection uses Symantec’s platform for information and analytic data processing across more than 200 million applications in more than 200 countries. Such information is used to define a security rating for each file accessed through the Internet and to create it. By that same way, it prevents targeted attacks and advanced persistent security risks with a degree of defense well beyond conventional anti-virus software capabilities.
https://www.broadcom.com/products/cyber-security/endpoint/end-user
References:
https://www.gartner.com/reviews/market/endpoint-protection-platforms/vendors
https://www.gartner.com/en/documents/3956420/magic-quadrant-for-endpoint-protection-platforms