G Suite is a Software as a Service (SaaS) suite of applications built and powered by Google. These cloud-based apps focus on different domains including business, collaboration, productivity, and education. Gmail, Docs, Sheets, Drive, Calendar, Google+, Slides, Forms, Sites, Hangouts and Keep are the main G-Suite tools offered by Google. G Suite is a valuable resource for businesses as well as individuals around the world.
G Suite was released as “Google Apps for Your Domain” 12 years ago. Gmail, Google Talk, Google Calendar and Google Page Creator (now known as Sites) were part of the initial launch. Two months later, Google Apps for education was also launched. Google’s application suite has included many tools and updates in the past 10 years. In September 2016 the company rebranded Google Apps as G Suite and launched its first hardware product “Jamboard” not long after that. The G Suite also includes the G Suite Marketplace (originally launched in 2010), which allows you to deploy third-party cloud applications for use in the G Suite collection.
Table of Content +
What can you do with Google G suite?
We invite you to read this article to know what you can do with the G Suite platform. This article will help to understand, how you can optimize the G Suite framework and use its products to better grow your business. G suite features including security and pricing details are also presented in this article.
A lot of the same Google applications would seem to be available for free, but there are some key features that make G Suite integrate perfectly with your business. G suite provides enterprise-level services to its customers although most of these items are free for everyone. Some of these features include optional unlimited cloud storage, shared calendars, advanced admin controls — such as adding and removing users, two-step verification, and single-sign-on — and simple data migration tools to transfer all the valuable data from your company to G Suite. Additionally, G Suite comes with mobile device management, allowing you to turn on / off mobile devices, monitor which applications are enabled, and remotely delete if the employee goes rogue on a company device.
G Suite Admin Console
The G Suite Admin Console helps business owners to handle anything conveniently from a single place. It has been overhauled and is even better than it was with Google Apps before.
you can do everything from adding new users and groups, handling devices, configuring security settings (like 2-factor authentication), introducing new custom domains that can be used with Gmail to your company.

Most of the apps in G Suite, if not all, have to be allowed by the administrator for use. Many of which are also available only in higher plans. If a function is not allowed, and a user tries to use it, they will see a message “not available”.
G Suite for Business and Education
There’s no doubt that G Suite is a powerful platform for businesses of all sizes. It is a digital tool in hand that facilitates organization, collaboration, efficiency, marketing, and sales. Follow this section as we explore how to set up G Suite for Enterprise, Business and Education. Let’s start with the pricing details.
Pricing
Google introduced a free standard edition of G Suite with reduced features until December 6, 2012, which was provided to those who signed up and registered their domain prior to the cut-off. G Suite has evolved and expanded immensely in the last ten years, without changing its costs.
Google has been offering two G Suite business options since day one: the G Suite Basic Version for $5 per user per month, and the G Suite Business Edition for $10 per user per month.
Now, the pricing depends on how many people who use the service are in the business, with each tier providing more functionality and capacity than the previous version.
G suite pricing for Business
There are three versions available for both small and large businesses.

Basic: 30 GB of shared Drive and Gmail storage for each user. Includes all of Google’s productivity features but excludes Cloud Search (the ability to browse through the content of your whole enterprise in G Suite), App Maker (build custom applications for your business) and Vault (G Suite data retention and eDiscovery). The minimum cost will be $6 per user per month.
Business: Generally same as the Basic plan but provides unrestricted storage for all users, including Vault, Cloud Search and Application Development. The business version costs $12 per user per month.
Enterprise: The Enterprise has all the same functionalities as Business version but incorporates enhanced security and administration monitoring, eDiscovery and prevention from data loss. Enterprise version cost is $25 per user per month.
G suite pricing for Education
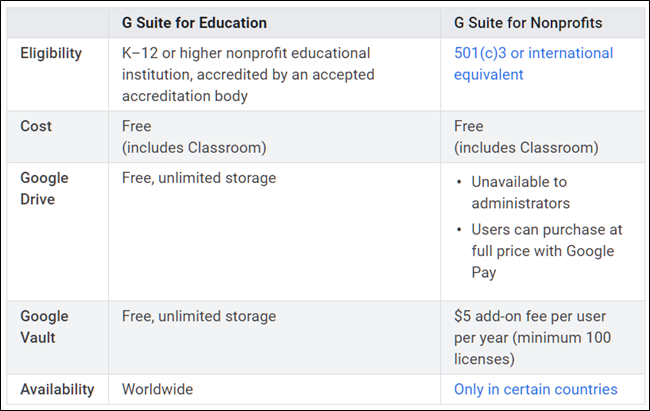
You can get G Suite Education for faculty and students if you administer an institution or are in charge of the decision making at your Institution. For your institution, G Suite Education has two versions.

G Suite for Education: G Suite for Education is free and will always be free that includes all the collaboration tools just like G Suite Basic but with additional Sites, Drive, and Gmail storage and free access to Google Vault.
G Suite Enterprise for Education: It offers advanced capabilities tailored for large institutions, with advanced technologies of enterprise level. It features advanced controls, improved analytics and search, and collaboration capabilities of a business-grade standard. Enterprise for Education costs faculty and staff $4 per user per month, and students $4 per user per month.
Ultimately, if you operate a non-profit organization, Google provides another free version for approved non-profits that has the same features and capabilities as the G Suite Basic edition that is highly comparable to the G Suite for Education edition.
Google Classroom:
This is where G Suite for Education diverges from standard G Suite Plans. Google Classroom is a virtual classroom meeting space. Users can add Google Docs learning materials, and students can all work in one place. Teachers will also give input directly at the Classroom to the students. Those are proprietary tools that follow the same rules as other services provided by Google. They may need to get used to it a little, but also multiple video tutorials are available.
G Suite for Education’s Prevention of Data Loss helps you to create policy-based guidelines that will be triggered when confidential information is found. Admins can set parameters to control which types of members of the information team can transfer from Team Drive. Hosted S/MIME is a security protocol that allows you to send stable, encrypted emails via Gmail, which is crucial if you want to exchange student data among staff members.
Privacy and Security with G Suite.
Security is the main concern about making the transition to cloud computing. And the reasons for that are pretty solid. With data leaks and rising cybercrime, IT experts are constantly under pressure to achieve excellence. G Suite protection is also debated as Google being the second-largest provider of cloud computing applications. There’s a lot of suspicion about the security of apps. It’s true that information stored in any cloud application is vulnerable if configured incorrectly. Yet it’s important to note that there are other ways Google’s cloud infrastructure is more secure and robust than the typical office server.
What do I need to know about security in G Suite?
Google states: “We do not store, inspect or use the G Suite data for advertising purposes and do not show ads in the core services of G Suite for Education or Government.” It claims that “the data brought into G Suite apps by businesses, schools and government departments is not Google’s. Whether it’s company intellectual property, confidential details, or a homework assignment, Google does not own that data and Google does not sell that data to third parties. Data is stored in Google’s data centers, built with custom-designed servers that run our own security and performance operating system, with more than 550 full-time security and privacy professionals.”
Google states that the benefits of using G Suite included “disaster recovery,” with data and information simultaneously replicated in two data centers at once so that if one data center fails, we can transfer your data almost instantly to the other center that reflects your actions as well. Although accepting that “no backup option is completely flawless from us or anybody else,” Google claims it has “invested a lot of effort to help make it second to none.” Encryption, specifically 128-bit or stronger AES, is applied to data while being stored in data centers, in transit between data centers and users, and between data centers.
In June 2014, TechCrunch announced at its introduction that as part of G Suite, Google Drive provides “enterprise-grade encryption and security,” like SSAE 16 / ISAE 3402 Type II, SOC 2-audit, ISO 27001 certification, commitment to Safe Harbor Privacy Standards, and promoting industry-specific criteria such as the Health Insurance Portability and Accountability Act ( HIPAA).
Here are some examples of ways how G Suite protects you and your information:
G Suite Admin: provides the user with the option to monitor how data is protected, view reports, and even control mobile device settings. G Suite administrators can also deny the right of employees to allow “less secure apps.”
Encryption (TLS): The G suite offers to transit e-mail encrypted messages.
Certs, audits, and assessments: G Suite routinely undergoes multiple impartial evaluations from third parties.
Data Retention: G Suite provides the ability to store, archive, search and export your information.
Privacy Policy: Google does not capture, check, or use the data for advertising purposes in G Suite services. No advertisements are allowed in all of the G Suite apps, too. You own your own personal information.
Transparency: Google actively focuses on transparency to keep users updated.
Important checklist to keep G Suite data safe in your company
Manage the Password strength of the users
First, the simplest G Suite security code is to help the staff pick a strong password — something with a complex combination of letters and numbers. As an administrator of G Suite, you get the ability to monitor and manage any user’s password strength in your company. You need to set criteria for minimum and maximum password strength requirements. By sharing opinions about how to build strong passwords, you can support your users. The best resource you have here form the Admin console is to monitor the strength of the users’ passwords. It provides you with a graph showing how good a password is for each user. You can get the weak ones easily modified.
Make 2 step verification compulsory.
Two-step verification is a method involving two authentication checks conducted one after the other to ensure that someone is who they claim to be. It offers the users an extra layer of protection by making them authenticate their password with a verification code. It can be in the form of messages, voice calls, notifications from smartphone apps and more. It means that no one can access your account even though your password gets leaked. As an administrator of G Suites in the company, you would like to implement 2-stage verification for all. Before the enforcement process, make sure everyone is enrolled in your company or they will get locked out of their accounts.
Don’t allow less secure applications to access user accounts
G Suite has a wonderful function to block sign-in attempts by applications and devices that do not comply with current security requirements. To do this,
Navigate to Security > Basic settings > Less secure apps
Tap “Disable access to less secure apps for all users”
when a malicious user uses a less secure app to enter a user’s account, end-users receive an email telling them that someone has tried to access their account from a non-secure app.
As an administrator for the G Suite, you may want to track when a user has enabled access to less protected applications. For this, head to the Account Activity Reports — it provides a Less Secure Apps Filter indicating that each user is denied access to less secure applications. Google can recognize apps that are less secure. As there are apps that do not use modern security requirements like OAuth 2.0. To access accounts programmatically they still use the old-school username/password authentication.
Manage access for third-party apps based on OAuth
A lot of incidents have occurred when non-Google apps impersonated Google ‘look and feel’ and gained access to data from your users. You could receive an e-mail stating ‘someone has invited you to edit the following document’ — you click the Open in Docs button — and you may land on a Google page requesting for permission. The email was sent from a non-Google app and a malicious program has just been whitelisted.
As a Gmail administrator, you wouldn’t want confidential information leaked out of Drive and Gmail from your users. For this reason, OAuth came into existence. With OAuth whitelisting, you will be able to choose specifically those third-party applications that should have access to the data of your users (Gmail, Drive, Calendar and Cloud Network Services); but the apps will still need permission from users to access their data. Once you have added that app to the whitelist of your organization, users may opt to grant or deny access to their data. There’s no way a malicious app can trick your users into allowing them access to your data.
Enable early detection of phishing
Email is still the most frequent carrier of phishing attacks. These emails may normally contain a link that leads the user to a website that is considered to be secure but are pure replicas of zero confidentiality. You don’t want these Phishing apps to get you in trouble. As a Gmail administrator, you’d like to apply an additional security layer to incoming emails—G Suite offers you ‘Early Phishing Detection.’ It uses machine learning to identify potential email threats. Gmail could give you a warning, or immediately move the email to spam. The moment Gmail senses malicious content in an incoming email, a transmission delay is added, and a thorough phishing analysis is performed.
Ensure unintended external reply warnings are on
If a user hits the reply, Google scans the receiver list, including those in Cc — to evaluate the possibility of data loss. If the recipient isn’t from your company, not on your contact list, and you’ve never spoken to them before, Google will display a warning to protect users from unintentional internal data leakage. If the receiver is intended, the user can simply dismiss the warning and proceed with the reply. This function provides a solid defense to the business against fake email messages and potential impersonation.
If you want to make sure that this option is on. Go to the admin console:
Apps > G Suite > Gmail > Advances settings Choose your top-level organization
Scroll to External Warning for Unintended Reply.
To activate or deactivate this function, Toggle the checkbox and click Save.
Remember that changes to user accounts can take up to an hour.
Limit the sharing of calendar information
There are many cases where people externally share their calendars so other users can plan and edit events. But, this is a threat to your data.
As a G Suite administrator, you would like to check how much calendar information people can exchange externally. You can monitor the level of calendar sharing with users outside the company and the default visibility of calendars internally.
External Sharing
If you limit external sharing for your company, users can’t surpass that limit while sharing events. For example, if you restrict the external sharing of your company to Free / Busy, Public Visibility events are shared only as Free/Busy. The other specifics of the event are kept secret.
Limiting Free/Busy sharing protects users from attacks by social engineering that depend on extracting information from the titles and attendants of meetings. Conversely, you can allow outsiders to access all material on the calendar and only select whether outsiders can or cannot alter calendar items or control the calendar.
Internal Sharing
Consumers can choose whether to share calendars with their colleagues. If a user does not configure their own calendar settings, the internal sharing options you set for your company will automatically apply. Even if the user’s calendar is internally visible to everyone, they will still be able to keep particular events private.
Be mindful of misconfigurations in Google Groups
In the past, some Google Groups have leaked sensitive information — emails that should never have appeared in public became searchable on Google. Kenna Security researchers say they discovered more than 9,600 organizations with the setting of a public Google Group and a third of them leaked sensitive emails somehow or other.
Even Google acknowledges that “a few instances have occurred when customers accidentally shared sensitive information due to misconfigured privacy settings in Google Groups.” So that’s why it’s critical that you keep a close look at unintended misconfigurations in Google Groups. Through the Admin console, you can check and update the permissions for sharing the domain — you can ensure that all groups of sensitive information are protected.
And if you give your users the option to build public groups, the domain-level environment will also be able to be switched to private. By doing so, you can be assured that no one outside of the company has access to a group that your users had previously set up to be public. If the company uses Google Groups to handle sales or support, you ‘d like to be able to be reached by a group from outside. This can be done without denying a public group the right to view topics.
As an administrator of the G Suite, you have the option to invite outsiders to post to a particular group — within the individual group setting. The setting applies regardless of whether group topics are set as private or public.